Azure Traffic Manager

Azure Traffic Manager
Azure Traffic Manager is a DNS-based traffic load balancer service, which enables you to distribute traffic to services across global Azure regions while providing high availability and quick responsiveness. In this article, I present what are the benefits of this service and how to use it.
Azure Traffic Manager uses DNS to direct client requests to the most appropriate service endpoint (“endpoint” is any Internet-facing service hosted inside or outside of Azure) based on a traffic-routing method and based on the health of the endpoints. This is a useful service for when you work with multi-region applications.
Routing Methods
Azure Traffic Manager provides a series of routing methods that determine how client requests are directed to different endpoints. They are:
- Priority: used when you need to route all user traffic based on priority. For example, you can have a primary endpoint for all the traffic, or provide multiple backup endpoints to direct traffic to another endpoint when the primary (or others) endpoint fails. For example, by default Traffic Manager will send all the traffic to the primary (the highest-priority) endpoint, and if the primary endpoint is not available, it will route the traffic to the second endpoint, and if the second endpoint is not available, it will route to the third, and so on. The priorities can be configured using values between 1 and 1000, where a lower value represents a higher priority. This can be useful to provide a fault backup service for disaster recovery scenarios.
- Weighted: used to distribute traffic across a set of endpoints based on their weight, which is informed by you. The weight can be configured using values between 1 and 1000, where the higher weight represents the higher priority.
- Performance: used when you have endpoints in different geographic locations and you want to direct users to the closest endpoint, for the lowest network latency.
- Geographic: used to direct users to specific endpoints based on the geographic location from which their DNS originated from. For example, you can define that all requests originating from East US must be redirected to West Europe, in order to only process data within West Europe (for legal reasons for example).
- Multivalue: used to return a list of all the healthy endpoints to the client. It does not support name servers or mapping for the endpoints, it only supports IPv4/IPv6 addresses.
- Subnet: used to map sets of end-user IP addresses range to a specific endpoint. For example, you can configure that all requests originating from a range of IP addresses will be redirected to West Europe, and the others go to another application.
Traffic Manager also brings some benefits such as:
- Endpoint Monitoring: Traffic Manager continuously monitors the health of the endpoints using health probes. If an endpoint becomes unavailable or unresponsive, Traffic Manager automatically redirects traffic to healthy endpoints, providing failover capability. This helps you to have high-availability applications that are resilient to endpoint failure, including Azure region failures.
- Metrics and Alerts: Traffic Manager allows you to use metrics (such as the number of queries that a Traffic Manager profile processes over a specified period, or the health status of the endpoints) and define alerts that can be triggered when certain conditions are met based on these metrics.
- Integration with Azure Services: Traffic Manager seamlessly integrates with various Azure services, such as Azure App Service, Azure VMs, Azure Traffic Manager Endpoint Monitor, Azure Functions, and more, allowing you to distribute traffic to different types of Azure resources.
- Traffic Manager Profiles: You configure Traffic Manager using a Traffic Manager profile, which defines the routing method, endpoints, health probes, and other settings for your application’s traffic distribution.
- Nested Traffic Manager: Traffic Manager allows you to nest Traffic Manager profiles in order to combine more than one traffic-routing method.
- Real User Measurements: by using the Performance routing method, Traffic Manager can look at where the DNS query requests are coming from and make intelligent routing decisions to direct those requestors to the Azure region that offers the lowest latency (this is done by using the network latency intelligence that Traffic Manager maintains for different end-user networks).
- Traffic View: provides information about your user bases and their traffic patterns at the granularity of DNS resolvers. With this service, you can understand where your user bases are located, can view the volume of traffic originated from these regions, can get insights into what is the representative latency experienced by these users and deep dive into the specific traffic patterns from each of these user bases to Azure regions where you have endpoints. For example, you can use Traffic View to understand which regions have a large amount of traffic but suffer from higher latencies, and with this information, you can plan your footprint expansion to new Azure regions.
Creating and Configuring a Traffic Manager Profile
For demonstration purposes, I created two ASP.NET applications and deployed them to two different App Services:
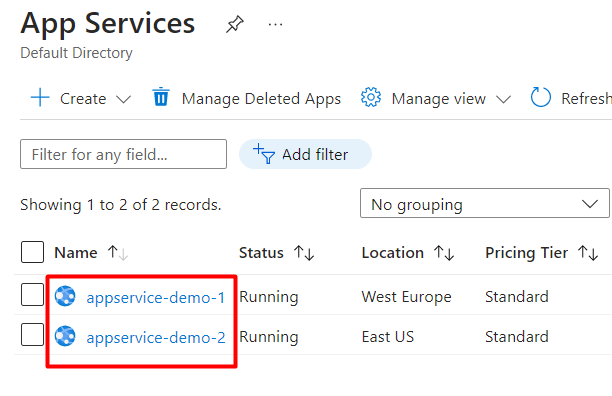
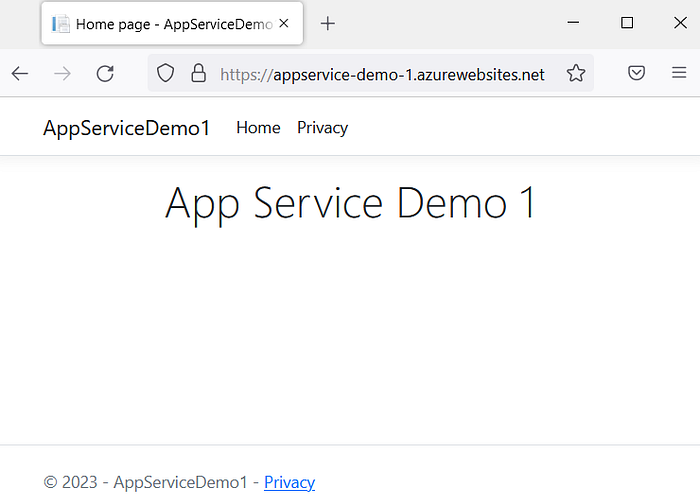
This is the App Service Demo 1 (appservice-demo-1.azurewebsites.net):
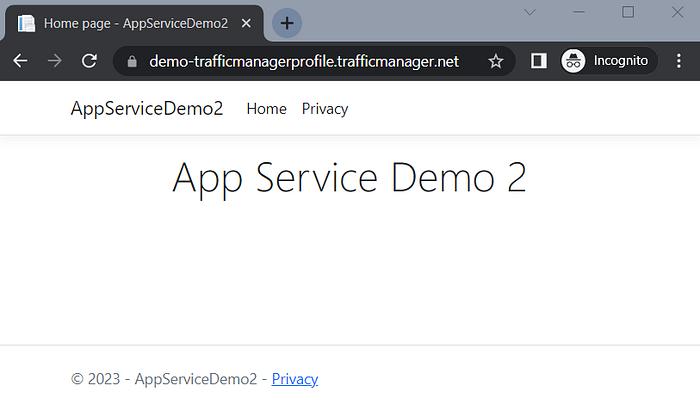
This is the App Service Demo 2 (appservice-demo-2.azurewebsites.net):

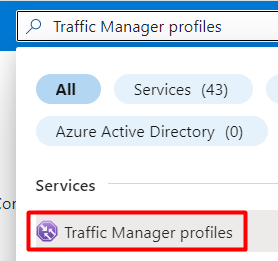
Now in Azure Portal, search for Traffic Manager profiles:
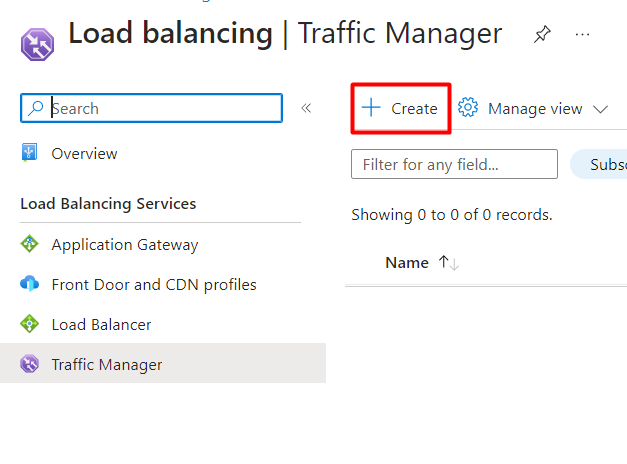
Then click on “Create”:
Add a name for your Traffic Manager profile, select the Routing method (in this example, I’m using the Priority), the Resource group and click on “Create”:
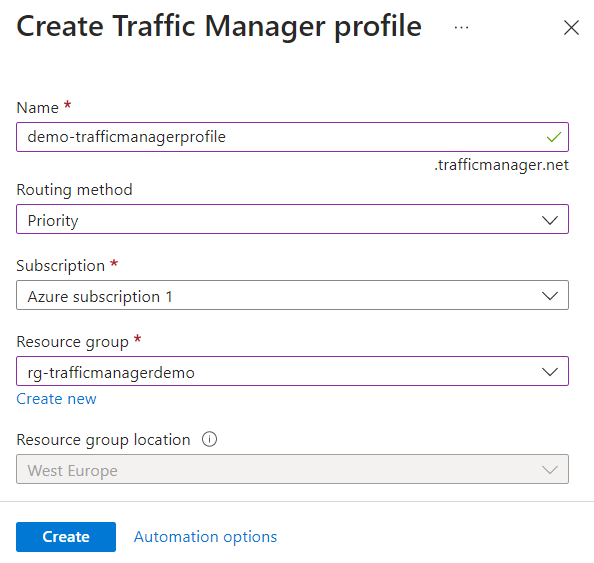
The Resource group location is disabled because this service is a global service, however, you need to inform the location of the resource group where the metadata associated with the Traffic Manager profile will reside. This will have no impact on the runtime availability of your profile.
Creating Traffic Manager Endpoints
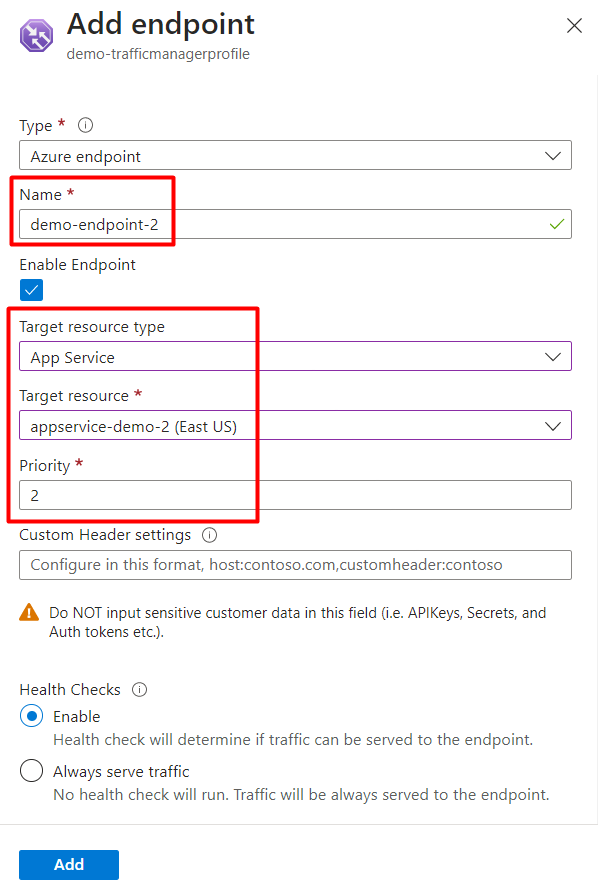
After your Traffic Manager profile is created, you need to create the Endpoint. For that, go to the service and select “Endpoints” and click on “Add”:

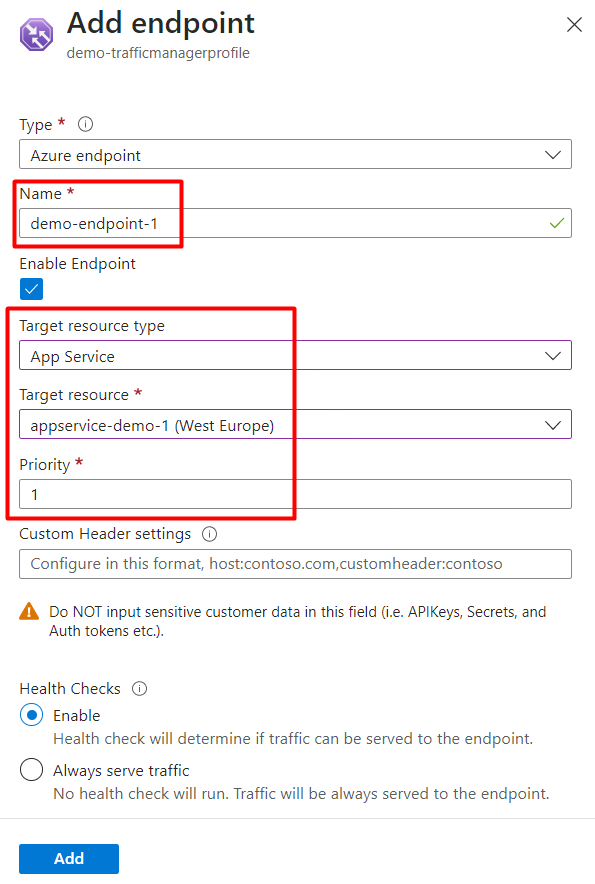
Then add a name for your endpoint and select the App Service and set the priority:
Then you should see your endpoints with the status “Checking endpoints”:
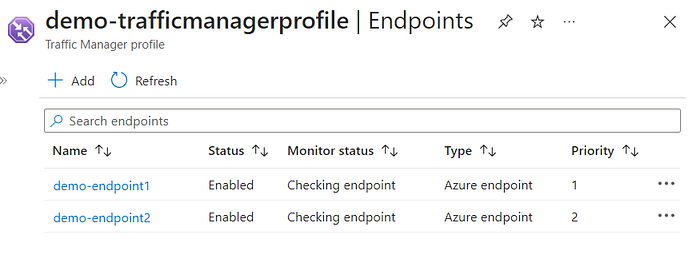
After a few minutes, your endpoints will be with the Monitor status as “Degraded” (as in the image below). The reason for this is because we still need to configure HTTPS, we are going to do this in the next topic

Just an extra information here, when I first saw this, I spend some time investigating and trying to understand why this was happening. I used the command below on Azure Portal (using PowerShell), to check the status that was being returned from my app service (this is because Traffic Manager execute some health probes checks to validate the endpoints), and I noticed that when I was using HTTP was returning 301 (Moved permantly), but when using HTTPS it was returning 200 — OK:
Invoke-WebRequest 'http://appservice-demo-1.azurewebsites.net' -MaximumRedirection 0 -ErrorAction SilentlyContinue | Select-Object StatusCode,StatusDescription
Invoke-WebRequest 'https://appservice-demo-1.azurewebsites.net' -MaximumRedirection 0 -ErrorAction SilentlyContinue | Select-Object StatusCode,StatusDescriptionBut when trying without HTTPS, got 301 (Moved Permanently):
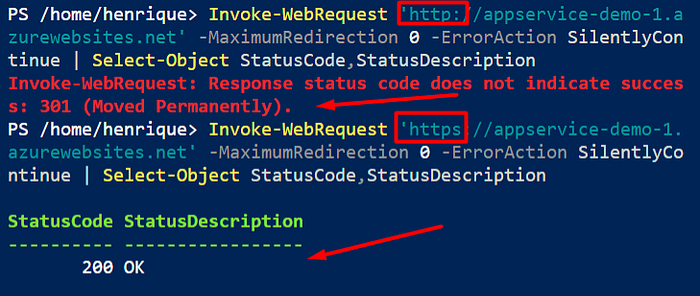
So this way I realize that HTTPS might be the cause for the Monitor status “Degraded”, and that was it indeed :)
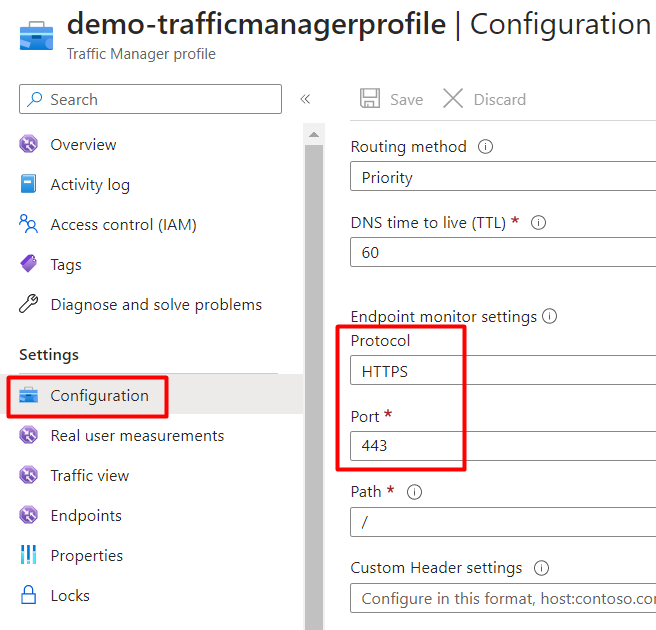
Configuring HTTPS for the endpoints
To configure HTTPS, in the Traffic Manager profile, go to the Configuration page and update the Protocol to HTTPS and the Port to 443:
After a few minutes, they will be with the status “Online”:
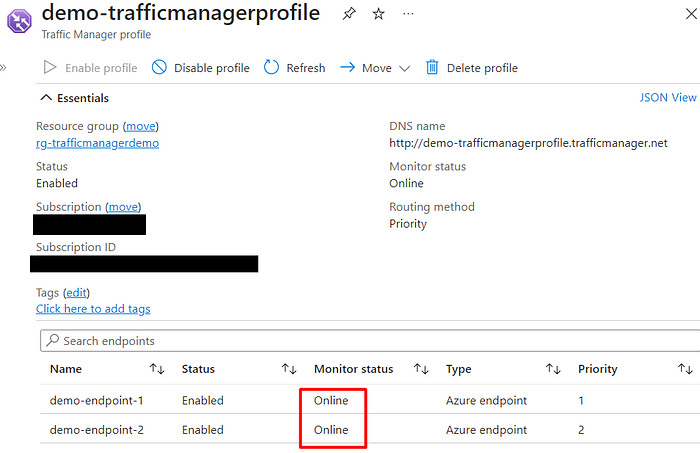
If you get the DNS from Traffic Manager and try to access it, it will complain about not being secure:
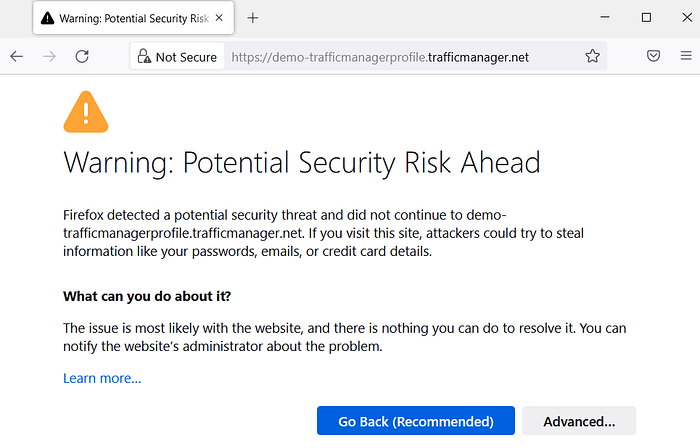
To fix that, we need to configure the App Services Certificates, which is exactly what we are going to do next.
Configuring App Services Certificates
To configure the certificate for the App Services, go to the App Service 1, and open the certificates page and click to add a new certificate:
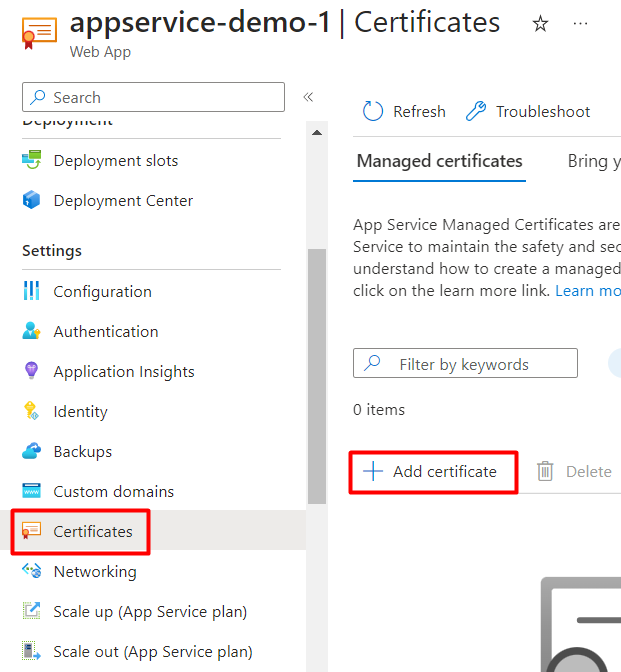
Then select the Custom domain and the Certificate friendly name and click on Validate, and then click on Add:
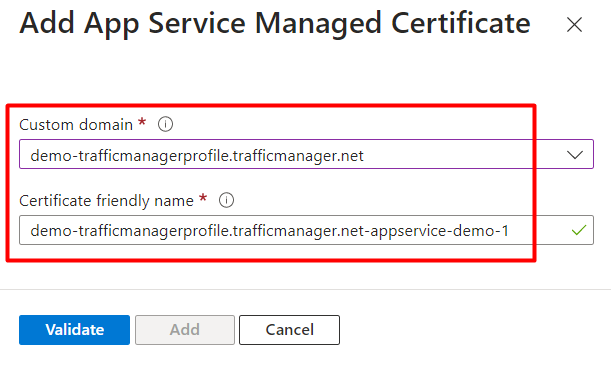
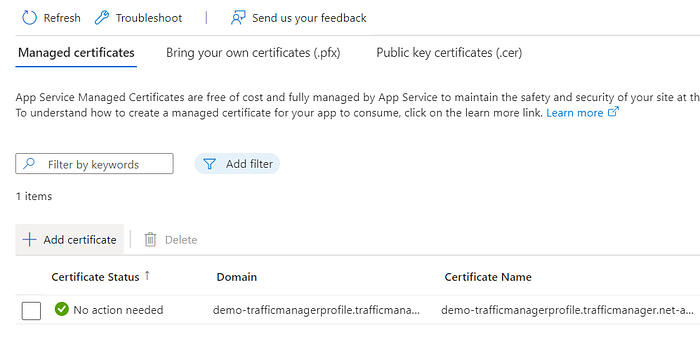
The certificate will be visible on your App Service certificates page:
Now go to the “Custom domain” page, and for the domain that has the status “No binding”, click on “Add binding”:

Then select the certificate and click on “Add”:
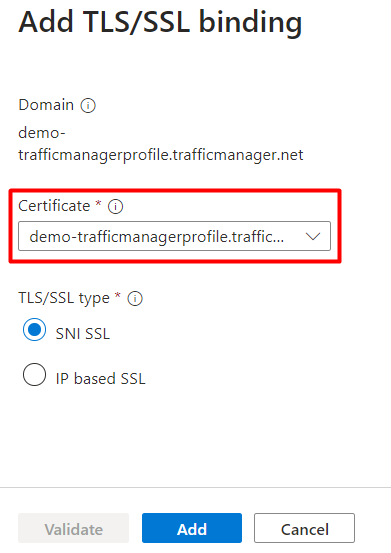
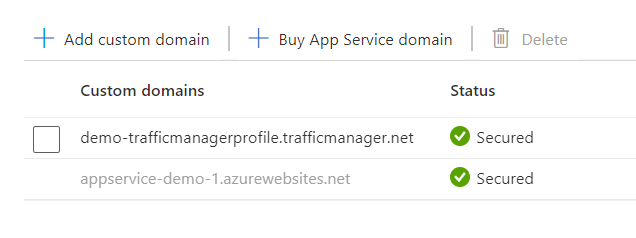
The status now should be “Secured”:
Now that you already have a certificate, you don’t need to create it again for App Service 1, however, you need to configure it to the custom domain. For that, go to the App Service 2, and go to the “Custom domains” page, and click on “Add custom domain”:
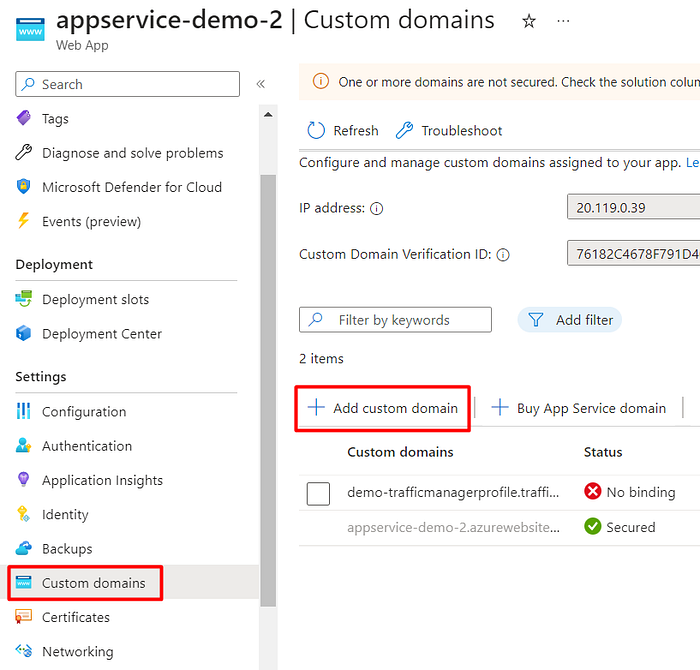
Then on Domain provider select “All other domain services” and in the “Domain” add the DNS from Traffic Manager (in this example is demo-trafficmanagerprofile.trafficmanager.net):

Then you should see it green:

Now let’s test the Traffic Manager. Get the DNS name and open it on a new browser page:
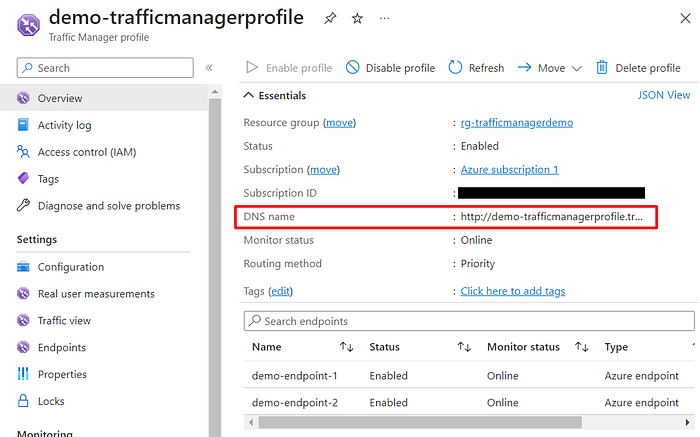
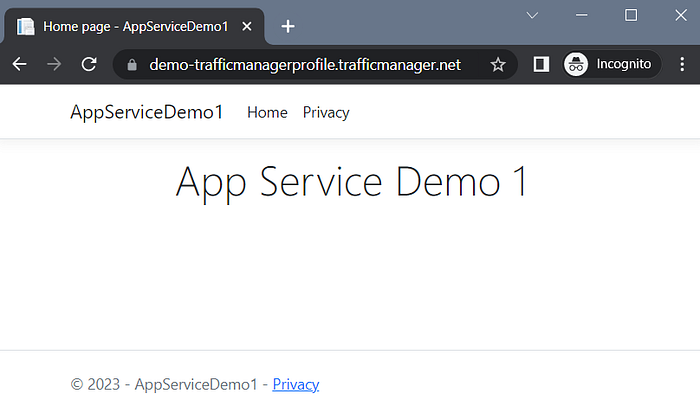
Access the website (https://demo-trafficmanagerprofile.trafficmanager.net/) and you will be directed to the App Service 1:
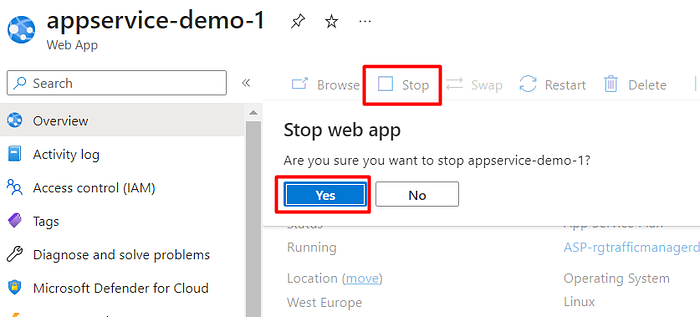
Now let’s stop the App Service 1 to simulate a failure:
Then you should see in Traffic Manager that endpoint 1 has Monitor status “ Stopped” and endpoint 2 has the status “Online”:
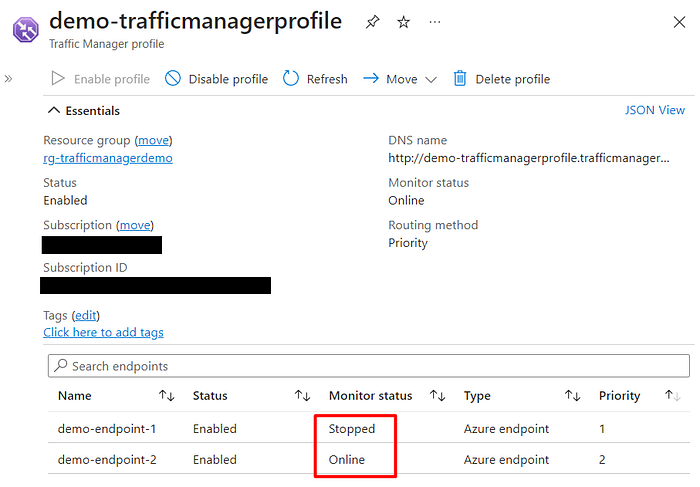
Try to access the app using the Traffic Manager DNS (ttps://demo-trafficmanagerprofile.trafficmanager.net/) again, and you will be redirected now to App Service 2:
Conclusion
Azure Traffic Manager offers flexibility and scalability for managing and distributing traffic to your applications across multiple services located in global regions. By leveraging intelligent traffic-routing methods and endpoint health monitoring, Azure Traffic Manager can direct client requests to the most suitable service endpoint, ensuring optimal performance and availability.